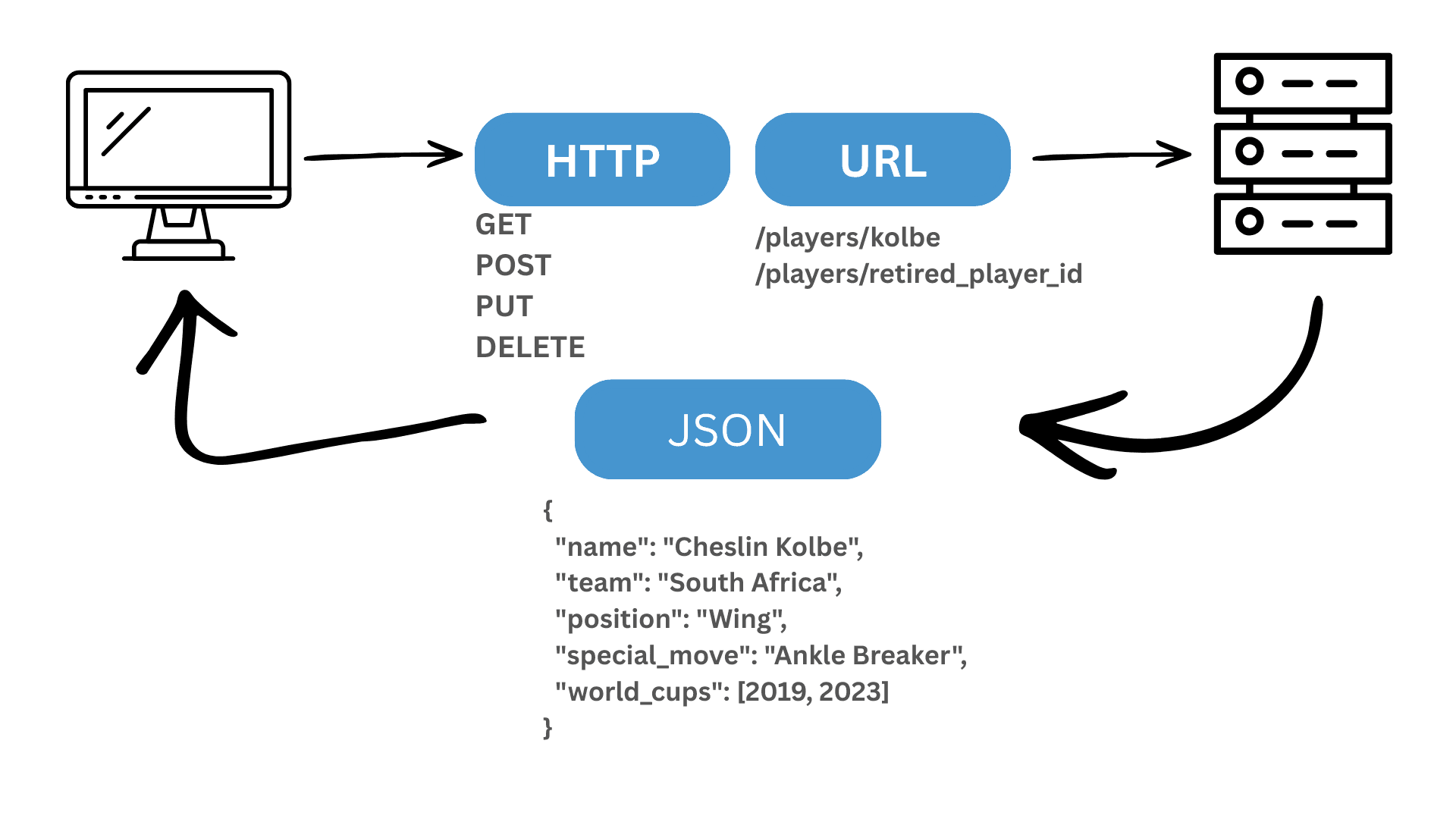
REST API Concepts, Illustrated with Rugby
In South Africa, rugby is not just a sport but a language many of us speak. Whether its the timing of a counter-attack in a Test match or the precision of a backline move involving Grant Williams, Sac
Search for a command to run...
In South Africa, rugby is not just a sport but a language many of us speak. Whether its the timing of a counter-attack in a Test match or the precision of a backline move involving Grant Williams, Sac
Modern development environments are powerful by design. That power comes with a trade-off that is often ignored in day-to-day work: third-party extensions running with local access to your machine. A
A fresh Ubuntu installation is designed to be permissive, catering equally to desktop, server, and container workloads without assuming a strict security model. However, the moment a system is exposed
With over eight years in the tech industry, I’ve learned a simple but uncomfortable truth. Effort compounds. The work you put in today pays off later in ways you cannot predict when you’re just starti
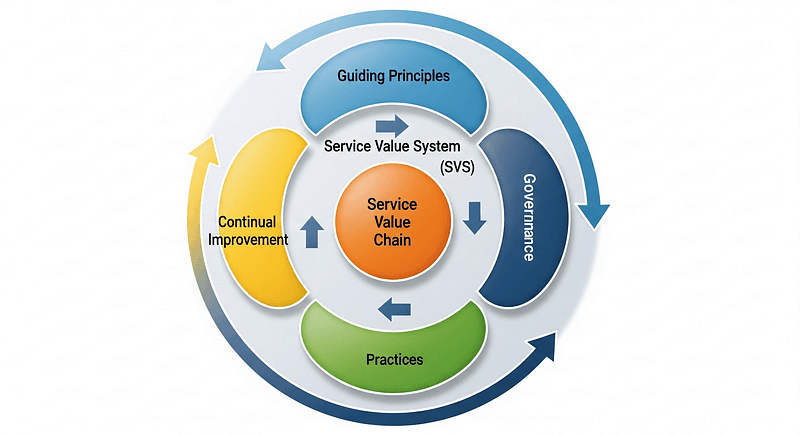
ITIL v4, or the Information Technology Infrastructure Library version 4, is a framework designed to help organisations manage their IT services effectively. It provides a comprehensive set of best pra
If you’ve ever spent hours deciphering someone else’s cryptic configuration, or frantically tried to recall that one crucial step you performed months ago, you’ll understand the silent agony of poor (
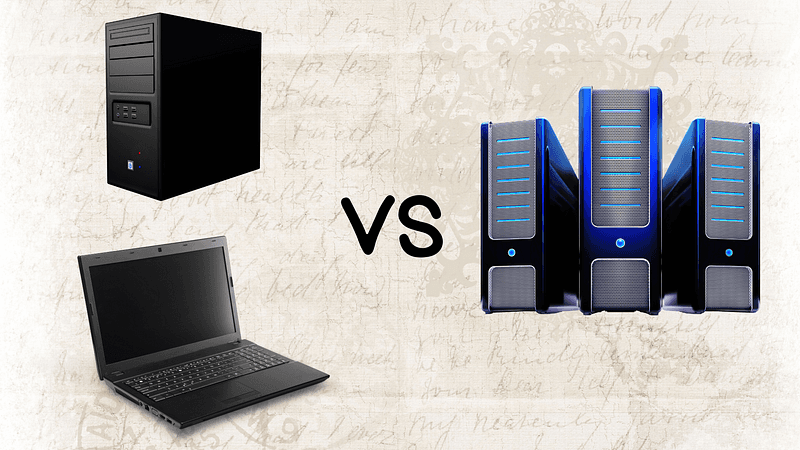
In computing, the terms desktop, laptop, and server are often used loosely, as if they’re interchangeable. But like comparing a sports car, a motorcycle, and a heavy-duty truck, each is engineered for
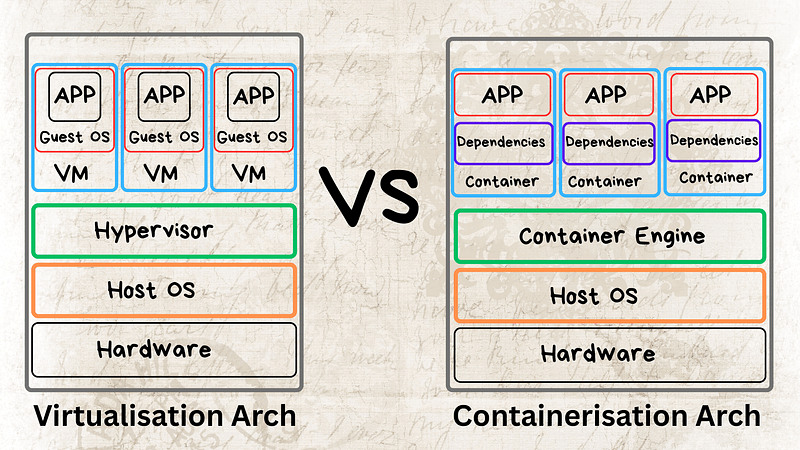
In the ever-evolving landscape of IT, the quest for efficiency, scalability, and resource optimisation has led to the widespread adoption of two powerful technologies: virtualisation and containerisat
ISO 27001 is an internationally recognised standard for Information Security Management Systems (ISMS). It provides a systematic approach to managing sensitive company information, ensuring its confid