Safeguarding yourself and your data in the Digital Age

Practical Steps to Protect Your Digital World
Protecting sensitive data is a combination of basic hygiene, informed decision-making, and using the right tools where they make sense. The goal is to reduce exposure, detect issues early, and limit impact when something does go wrong.
1. Navigate the Web Safely
Use privacy-focused browsers: Browsers such as Brave, Firefox, or Vivaldi with strict tracking protection reduce exposure to third-party scripts and advertising networks that are commonly abused for malvertising. This lowers the chance of drive-by downloads and silent redirects.
Inspect links before interacting: Hover over links to confirm the destination URL before clicking. Look for subtle misspellings, extra subdomains, or unfamiliar domains. On mobile devices, long-press the link to preview it.
If you receive an unexpected attachment or download, scan it using a service like VirusTotal. This allows you to see whether multiple security engines flag it as malicious before you execute it.Use protective DNS resolvers: Switching to a security-focused DNS provider such as Quad9 or Cloudflare can block known malicious domains before a connection is even established. This is a low-effort control that works across all applications, not just the browser.
2. Defend Against Social Engineering
Verify requests using a separate channel: If you receive an urgent request for money or data, call the person or message them on a different platform to verify. Never use the contact details provided in the suspicious email.
Check the actual sender identity: Email display names can be spoofed. Always inspect the full email address, especially for financial or account-related messages.
Be cautious with urgency and pressure: Messages that demand immediate action are often designed to bypass normal judgement. Take time to verify before responding.
Validate breaches and claims: If you receive a message claiming your account has been compromised, confirm it independently using services like Have I Been Pwned. This helps distinguish real incidents from scare tactics.
3. Secure Your Credentials
Use a password manager: Tools like Bitwarden or 1Password generate and store strong, unique passwords. This removes the need to reuse credentials across services.
Use stronger multi-factor authentication: Avoid SMS-based codes where possible due to SIM swap risks. Prefer authenticator apps or hardware security keys. These methods are tied to your device rather than your phone number.
Monitor credential exposure: Periodically check if your email addresses or passwords have appeared in known breaches using services like Have I Been Pwned. If found, rotate those credentials immediately.
4. Harden Your Systems
Keep systems updated: Enable automatic updates for your operating system and applications. Many attacks rely on known vulnerabilities that already have patches available.
Full Disk Encryption: Ensure FileVault (macOS) or BitLocker (Windows) is active. Without this, a thief can read your files simply by plugging the hard drive into another computer.
Use endpoint protection: A modern antivirus solution with real-time protection and ransomware detection adds a layer of defence against common threats. Built-in solutions are often sufficient when properly configured.
Limit administrative access: Operate daily tasks as a standard user where possible. This reduces the impact of malicious code execution.
5. Secure Your Network Access
Be cautious on public networks: Public Wi-Fi networks can be monitored or manipulated. If you must use them, ensure websites use HTTPS and consider a reputable VPN such as ProtonVPN or an OpenVPN-based provider to encrypt your traffic.
Secure Your Home Router: Change default credentials, disable remote management, and ensure firmware is up to date. The router is a critical control point for all devices on your network.
6. Data Resilience and Backups
The 3-2-1 Strategy: Maintain three copies of your data, stored on two different media types, with one copy offline or off-site. This protects against hardware failure, accidental deletion, and ransomware.
Test your backups: A backup is only useful if it can be restored. Periodically verify that recovery works as expected.
Separate personal and work data: If using corporate systems or cloud storage, keep personal data separate to avoid compliance and access control issues.
7. Reduce Your Digital Footprint
Review application permissions: Regularly check which apps have access to location, microphone, camera, and contacts. Remove permissions that are not required.
Limit exposed personal information: Set social media profiles to private where possible. Avoid sharing details that are commonly used in account recovery processes.
Clean up unused accounts: Old accounts increase your attack surface. Delete services you no longer use, especially those linked to stored payment details.
8. Use Free Verification and Analysis Tools
These tools provide quick validation without requiring deep technical knowledge:
Have I Been Pwned
Check if your email addresses or passwords have appeared in known data breaches.VirusTotal
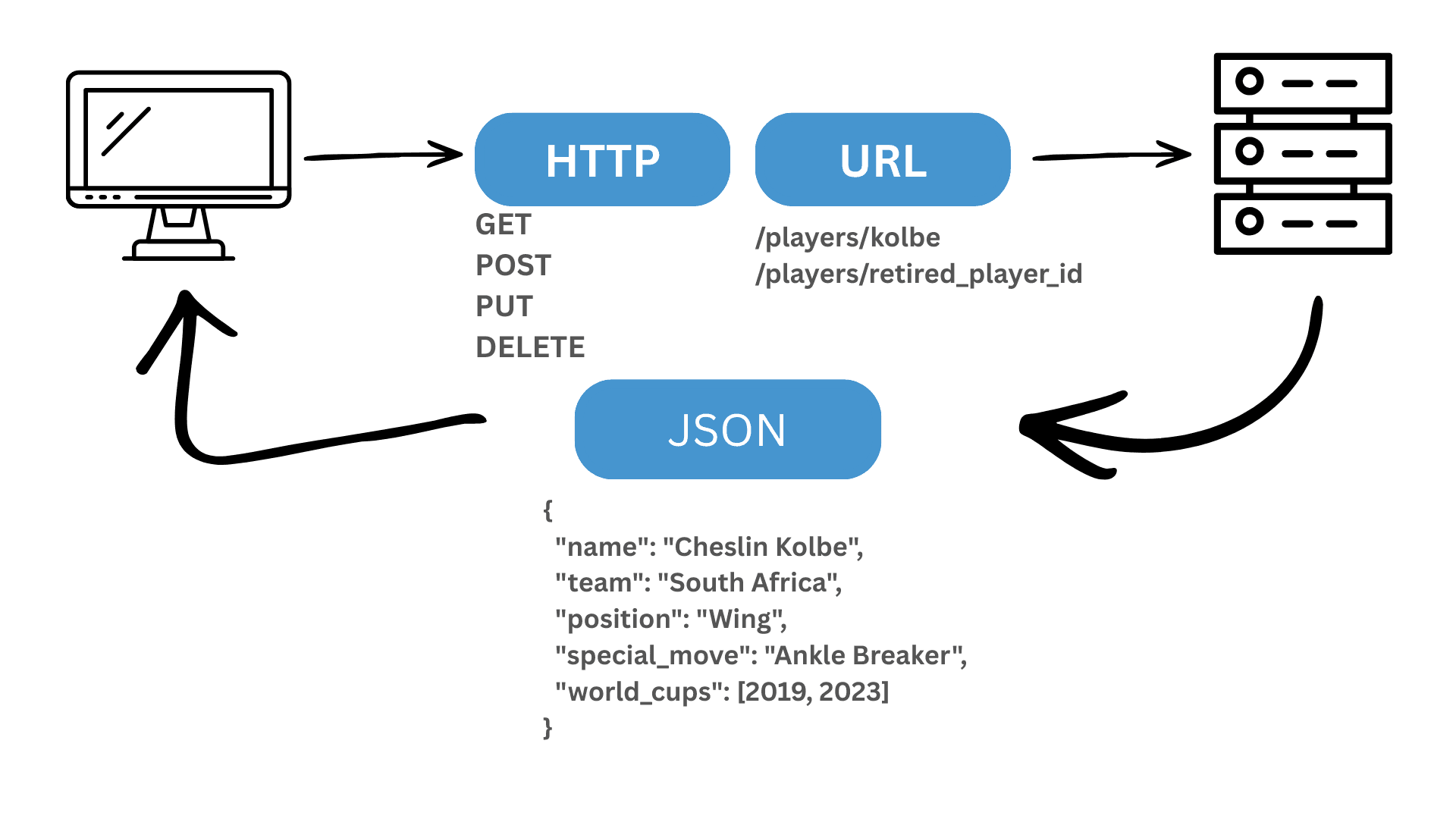
Upload files or submit URLs to scan them against multiple security engines before opening or visiting them.Browser developer tools or online header checkers
For more technical users, inspecting HTTP headers or certificate details can help validate whether a site is legitimate.WHOIS and domain lookup tools
Useful for identifying newly registered or suspicious domains often used in phishing campaigns e.g Cisco Talos.
The common thread across all of this is consistency. None of these steps are complex on their own, but applied together they significantly reduce risk and improve your ability to detect and respond to issues early.